
Wireless sensor networks (WSNs) have garnered much attention in the last decades. Nowadays, the network contains sensors that have been expanded into a more extensive network than the internet. Cost is one of the issues of WSNs, and this cost may be in the form of bandwidth, computational cost, deployment cost, or sensors’ battery (sensor life). This paper proposes a dual-level sensor selection (DLSS) model used to reduce the number of sensors forming WSNs. The sensor reduction process is performed at two consecutive levels. First, a combination of the Fisher score method and ANOVA test at the
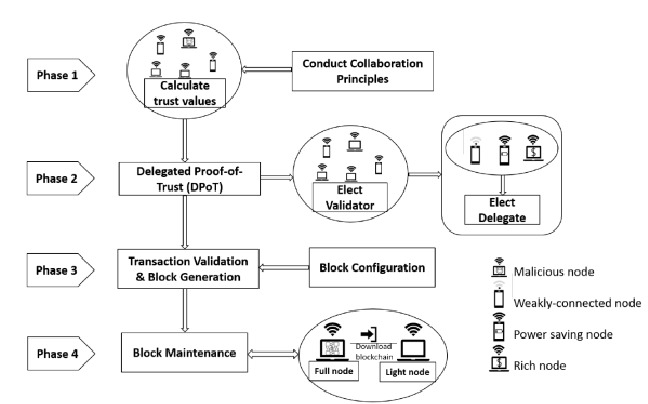
Many systems have recently begun to examine blockchain qualities in order to create cooperation enforcement methods. This paper provides a complete and extensive evaluation of work on multi-hop MANETs with blockchain-based trust control between nodes. We contextualize the snag of security in MANETs resulting from the lack of trust between the participating nodes. We present the blockchain concepts and discuss the limitation of the current blockchain in MANETs. We review the promising proposed ideas in the state-of-the-art based on research papers. Finally, we discuss and summarize strategies
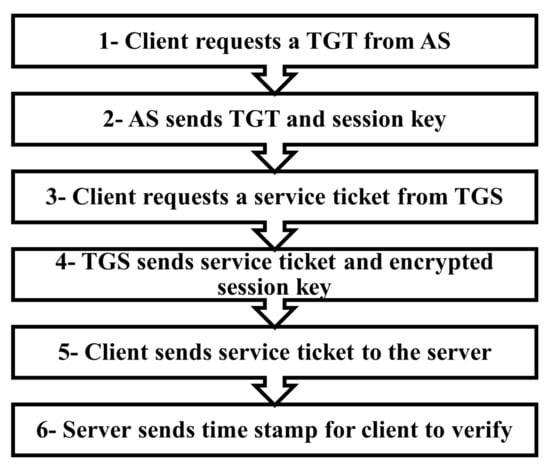
Active Directory Domain is a Microsoft service that allows and facilitates the centralized administration of all workstations and servers in any environment. Due to the wide use and adoption of this service, it has become a target for many attackers. Active Directory attacks have evolved through years. The attacks target different functions and features provided by Active Directory. In this paper, we provide insights on the criticality, impact, and detection of Active Directory attacks. We review the different Active Directory attacks. We introduce the steps of the Active Directory attack and
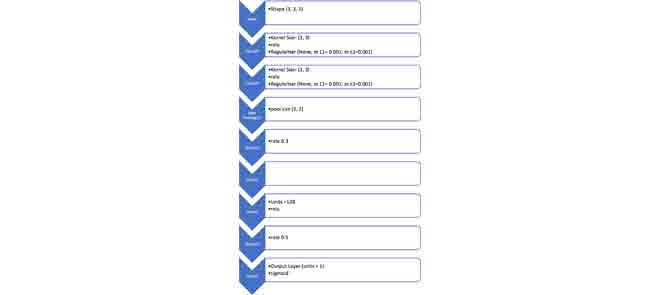
The fast expansion of the Internet of Things (IoT) in the technology and communication industries necessitates a continuously updated cyber-security mechanism to keep protecting the systems' users from any possible attack that might target their data and privacy. Botnets pose a severe risk to the IoT, they use malicious nodes in order to compromise other nodes inside the network to launch several types of attacks causing service disruption. Examples of these attacks are Denial of Service (DoS), Distributed Denial of Service (DDoS), Service Scan, and OS Fingerprint. DoS and DDoS attacks are the
A recommender system is a set of tools for information retrieval. It improves access and proactively recommends items and services that match users' tastes by considering their explicit and implicit preferences and behaviors. Recommender systems have become very popular in the e-commerce field. Today, the internet is flooded with diverse information that makes it very difficult for the end-users to reach out for what they need. Recommender systems provide tailored views to users who are constantly adapted to the users' changing tastes. Although many recommendation techniques have been
Computers and systems are vulnerable to many threats. Security researchers identified the malware as the major computers and systems threat. Malware can be classified into different types depending on the infection, attacking target, and persistence technique. In this paper, Malware detection techniques are observed with the identification of each technique's strengths and weaknesses points, followed by a comparison between all malware detection techniques. © 2022 IEEE.
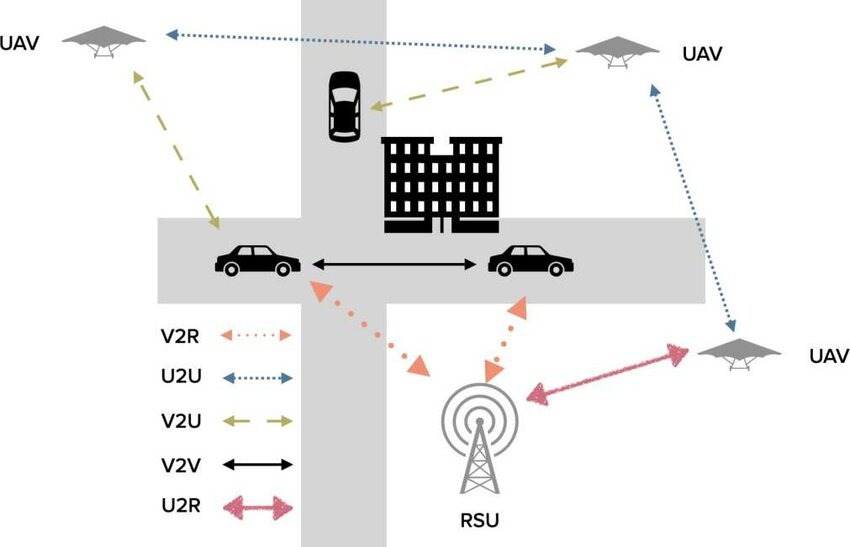
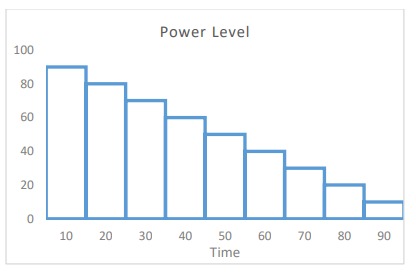
Mobile Ad hoc networks (MANETs) facilitate the communication of devices with a limited communication range. A MANET can be described as a decentralized network with a constantly changing topology. This makes it vulnerable to different attacks. The black hole is one of the most dangerous attacks in MANETs. This paper discusses the Blackhole attack in a random mobility environment and analyses its impact on MANETs using several parameters for single and multiple connections. © 2022 IEEE.
There are many novel techniques for intrusion detection in vehicular ad hoc networks and autonomous and connected vehicles. Detecting and reporting an attack is the main responsibility of an Intrusion detection system (IDS). Deep learning is used to make IDS smarter and more accurate. It implies other challenges on the other hand. This paper covers the proposed IDS based deep learning solutions and comparing effectiveness and efficiency of those solutions. © 2022 IEEE.
There are many situations where there is a need for certain devices to be connected in a network independently without having a heavy infrastructure or human interventions to configure and connect them. This type of network is called ad-hoc networks. The key concern with such networks is how nodes communicate with each other and exchange information efficiently and securely. The issue with ad hoc networks is that traditional routing protocols are not suitable for such networks. In this paper, the performance of specific routing protocols for ad hoc networks will be evaluated. © 2022 IEEE.
The widespread manufacturing of traditional plastics and their use in various commercial applications endangers both fossil fuel sources and the environment. Bioplastics have emerged from the development of renewable resources to provide sustainable solutions. These polymers are more acceptable than conventional plastics because they use renewable resources such as agricultural wastes (rather than petroleum sources) and are biodegradable under various conditions. The physical and chemical structure of bioplastics significantly affects their biodegradability, and their environment plays a